5 Common Types of Phishing Attack
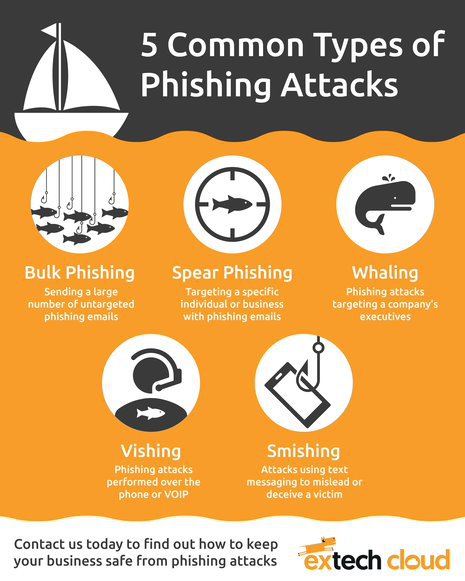
5 Common Types of Phishing Attack
https://extechcloud.com/wp-content/uploads/2022/05/Types_of_phishing_attacks.jpg
To support organisations with cybersecurity in the cloud, Extech Cloud keeps up to date with developments in cybersecurity and compliance, including cybersecurity threats. Phishing attacks, for example, have become more sophisticated in recent years, with more opportunities to attack through multiple devices. Here are five common types of phishing attack to be aware of.
What is a phishing attack?
You have likely heard of phishing attacks before. It is when an attacker sends a fraudulent message designed to trick a person into revealing sensitive information, or to deploy malicious software (or ransomware) on the victim’s infrastructure.
Bulk phishing
Bulk phishing is when the attacker sends a large number of untargeted phishing emails, often impersonating banks or financial service providers, to individuals and employees. Bulk phishing is the most common type of phishing attack.
Spear phishing
Spear phishing takes a more targeted approach. The email will include tailored communication to target a specific organisation, or even a specific individual in an organisation. This can make it appear more like a legitimate email.
Whaling
Like spear phishing, whaling is targeted approach, with the attacker’s sights set on the big fish’. A whaling phishing attack targets specific executives, high-level decision makers, CEOs, and CFOs, for example, in an individual organisation.
Vishing
Vishing (also known as voice phishing) uses the telephone or VOIP system. The attacker will often call multiple telephone numbers, mimicking a bank or other trusted organisation, and play a recorded message about an issue with an account or credit card. They will then attempt to encourage the victim to call another number to resolve the issue’, where they will then ask for sensitive information.
Smishing
Smishing (also known as SMS phishing) uses text (SMS) messages to target individuals. Similar to email phishing, the message will ask the victim to click a link, call a phone number, or contact an email address, where they will often be asked to share sensitive information.
If you want to discuss your cybersecurity requirements, contact Extech Cloud today. You can also ask about our no-obligation, feasibility study.
Back to News & ResourcesRelated news
Book a free online consultation
We love talking to businesses and understanding what they do and what they need. If you'd like to book a short, no obligation consultation, please provide us with your details. We understand that you may already have an IT company, consultant or team, so all contacts are treated as completely confidential. A fresh new IT approach could begin here...
Keep connected
Newsletter signup
News & Resources
Get latest updates, downloads and white papers.

